How to reach Wethenorth market safely in 2026
Eight steps. From zero to a working Tor connection, a verified link, and an invitation to Canada's only domestic-only privacy network market. Read the whole thing once before you start. There are no shortcuts worth taking here — phishing sites targeting Canadian WTN users exist specifically because buyers rush.
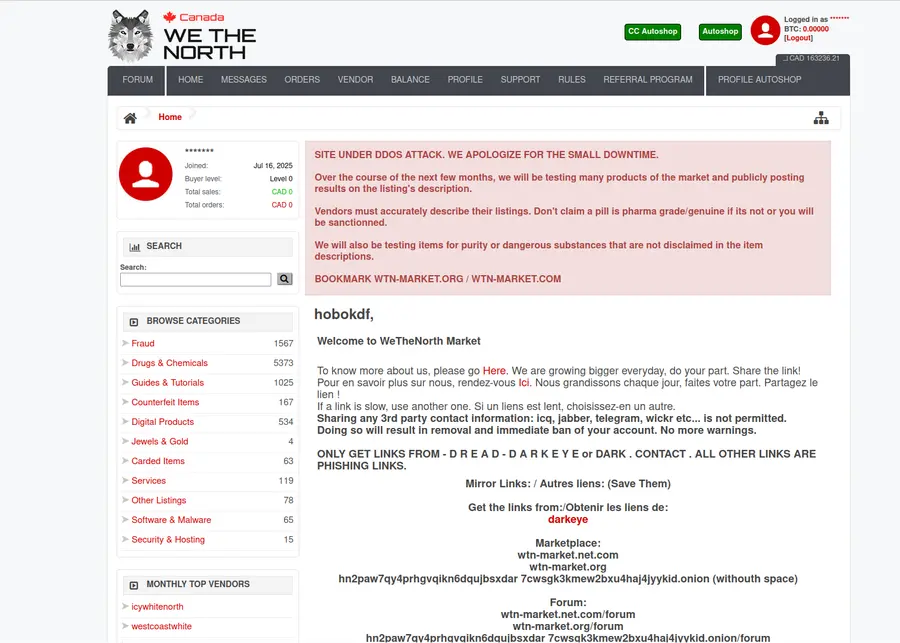
Wethenorth market launched in 2021. It is region-restricted to Canada and North America. Registration is invite-only. All 300 vendors ship domestically — package never crosses a border, no customs inspection. Two verified .onion mirrors exist as of April 2026. This guide covers everything from installing Tor Browser to making a first purchase. For general background, read the origin story page. For both verified mirrors with copy buttons, visit the mirrors directory.
Install Tor Browser from the official source
Download Tor Browser from torproject.org. That URL. No third-party mirror, no Chrome extension, no app store listing that claims to package it. The Tor Project is the only authoritative source. On Windows, verify the SHA256 hash published on the download page before running the installer. On macOS, drag it to Applications. On Linux, extract the archive and run the included script.
Tor Browser is the only software that resolves .onion hostnames. Regular Chrome, Firefox, or Edge cannot reach them at all — they'll return a DNS error. Wethenorth market addresses end in .onion. You need this browser. Close all other browser windows once Tor Browser is open; a stray session leaking DNS lookups through your regular browser is the single most common operational mistake among new buyers.
The download takes about three minutes on a standard Canadian broadband connection. The installed footprint is under 150MB. It does not interfere with your regular browser profile.
Download verification: the Tor Project publishes a cryptographic signature alongside each installer. Use GnuPG to verify it before running. One step, under two minutes, eliminates the risk of a tampered installer entirely.
Raise the security slider to Safest
Click the shield icon in the Tor Browser toolbar. Select Safest. This disables JavaScript, disables WebGL, blocks most fonts, and restricts audio and video APIs. The Electronic Frontier Foundation documents the privacy implications of each setting: every active scripting engine is a potential fingerprint vector. Wethenorth market was built to function without JavaScript. The interface renders fine in Safest mode.
Also turn off: HTML5 geolocation, browser autofill, and any hardware acceleration. Never install a single add-on or extension inside Tor Browser. Tor's anonymity depends on all users looking identical. The moment you customise the browser — even one extension, one changed font, one about:config preference — your fingerprint stands out from the 2+ million other users worldwide. Boring is safe. Boring is the point.
The Safest setting is global. It persists across sessions unless you change it back. Set it once and leave it.
What breaks at Safest: some clearnet sites fail to load because they require JavaScript. That's expected. .onion services designed for privacy — including Wethenorth — are intentionally built without JS dependency. If a site insists you enable scripting, treat that as a warning signal.
Copy a verified link — never type it
Use the copy button in the sidebar on this page, or visit the mirrors directory for both verified addresses. Hit Copy. Paste into Tor Browser. Done. Do not type a 56-character onion address manually. Do not search for it on DuckDuckGo or Google. Do not copy it from a screenshot, a Reddit post, or a Telegram group.
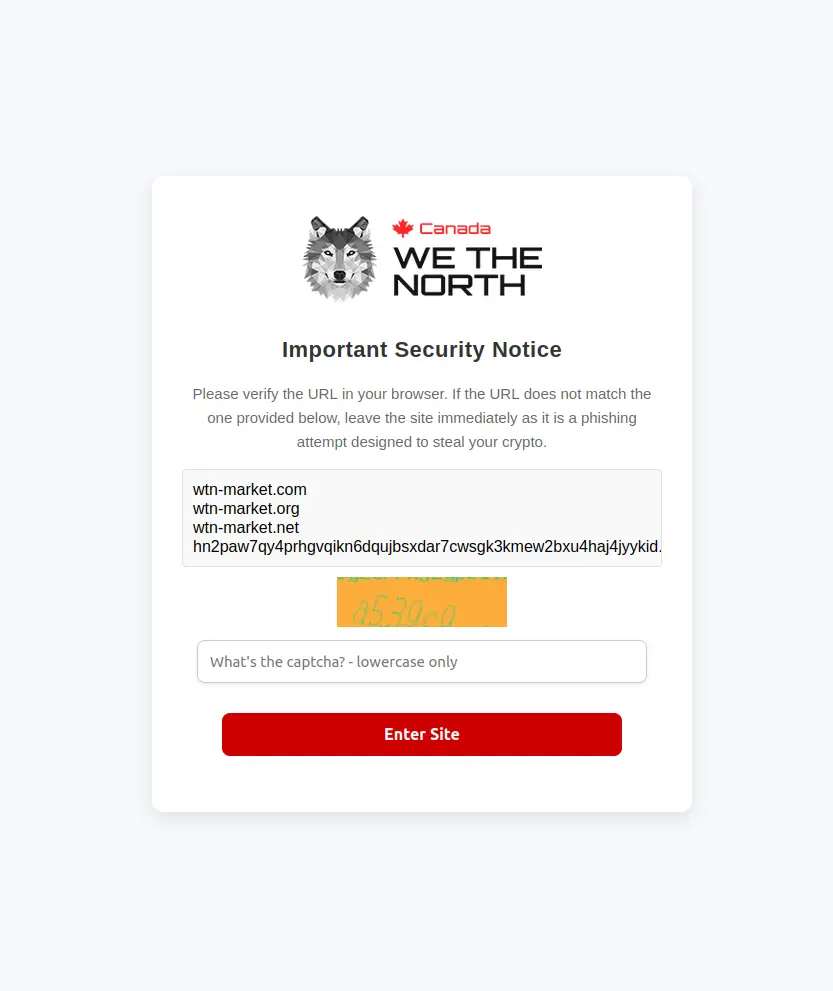
Phishing sites targeting wethenorth market users exist specifically to catch people who type or search instead of verifying. The addresses look identical to the real ones — a single transposed character in the middle section redirects you to a clone built by criminals who record your login credentials. As Privacy Guides notes: for any onion service, the verification step takes ten seconds and prevents the most common attack vector entirely.
After pasting, visually check the first four and last four characters against what you copied. Both WTN mirrors start with hn2p. If the string you're about to visit doesn't start with those four characters, do not proceed.
Cross-check method: the /d/WeTheNorth subboard on Dread publishes PGP-signed mirror announcements from the admins. Import the WTN public key into GnuPG and verify the signature. If the address in the announcement matches this page, you're looking at the real market.
Paste into Tor Browser and wait for the circuit
Tor routes your connection through three volunteer-operated nodes before it reaches the destination. Building that circuit takes 10 to 30 seconds. If the page doesn't load on the first attempt, press Ctrl+R and wait again. Do not assume the mirror is unreachable after a single timeout.
Both Wethenorth mirrors are load-balanced. One circuit occasionally stalls while the other works. If both mirrors time out after five attempts each, the Tor network may be under external stress — not the market. Right-click the address bar, select New Tor circuit for this site, and try once more. Morning hours in North American time zones typically have the fastest connections.
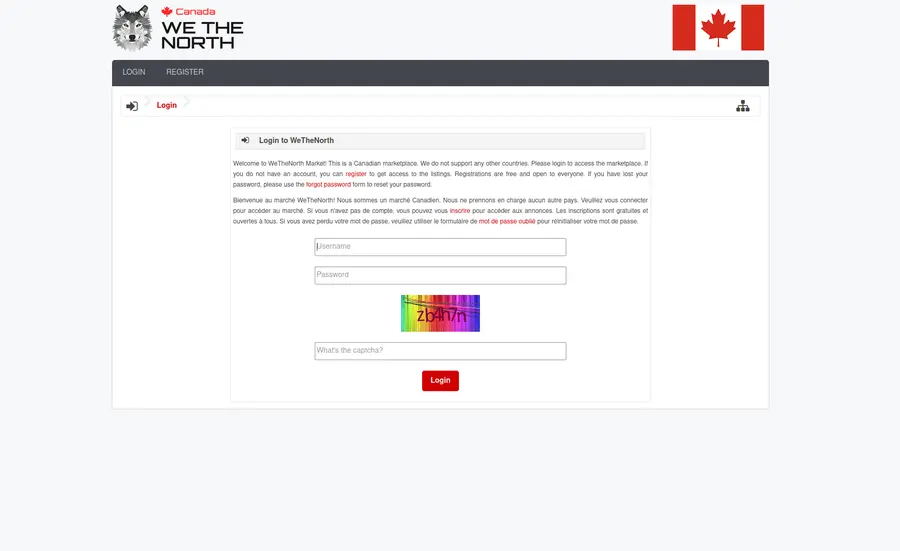
When you land on the real Wethenorth market, the login card and captcha render without requiring scripts. There is no complex animation, no loading spinner, no JavaScript-dependent element. The static, minimal interface is one of the real signatures of the platform. A page that requires you to enable scripting to proceed is almost certainly not WTN.
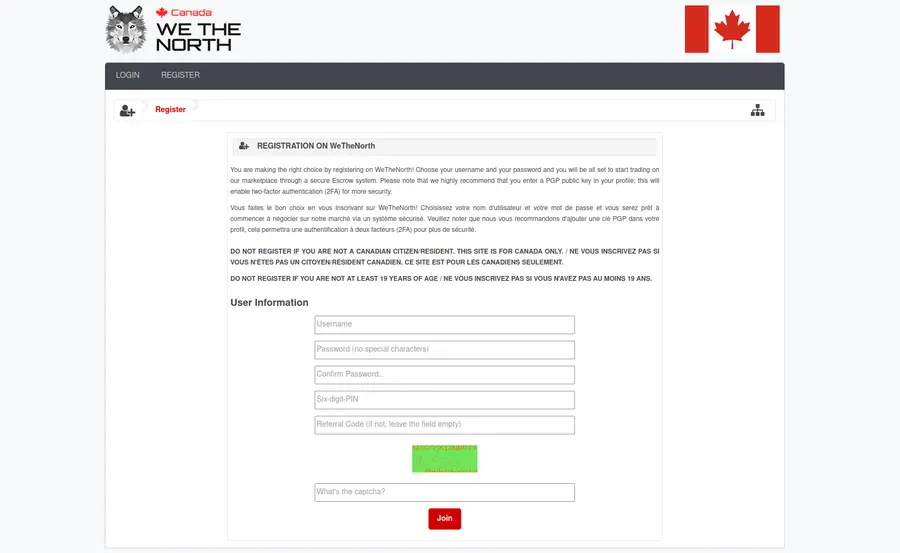
Obtain an invitation from a vetted source
Wethenorth market uses invite-only registration. You cannot create an account without a valid invitation code from an existing member in good standing. This gate is the primary reason the community has stayed functional and lower-profile since 2021.
The standard approach: join the Dread forum and become a regular participant in the /d/WeTheNorth subboard and related Canadian privacy network communities. Answer questions, comment on vendor reviews, engage with ongoing discussions. Members with a few months of post history and a visible track record of legitimate participation get invited within a few weeks of asking. Accounts created yesterday asking for codes on day one get ignored.
Never pay for an invitation. Anyone selling codes in Telegram, Signal, or Reddit is running a scam. Invitation codes do not have monetary value to legitimate members — they are extended as a community favour, not a transaction. The moment payment enters the picture, you're dealing with someone who fabricated the code or is trying to extract money from you before disappearing.
It's a social filter. It has kept Wethenorth's user base measurably safer than any open-registration global competitor. The patience required is the fee of admission.
Set up a Monero or Bitcoin self-custody wallet
Wethenorth accepts both Monero (XMR) and Bitcoin (BTC). Monero is the privacy-first option: transactions are untraceable by design at the protocol level. Bitcoin offers broader exchange availability and is fine for buyers who are already holding it, though the transaction graph is publicly visible on the blockchain.
Acquire XMR through an exchange that supports Monero withdrawals — most major Canadian exchanges do not, so you may need to use a privacy-focused exchange or convert through a swap service. Read the Monero Project documentation before your first transaction. Cake Wallet is the standard mobile self-custody wallet for XMR. Feather Wallet covers desktop. For BTC, Electrum or BlueWallet.
Critical rule: never fund your Wethenorth deposit directly from an exchange wallet. Always withdraw to a self-custody wallet first, then transfer from that wallet to the market. Exchange-to-market transfers leave a direct, documented link between your verified exchange identity and the market deposit. An intermediate self-custody step severs that link.
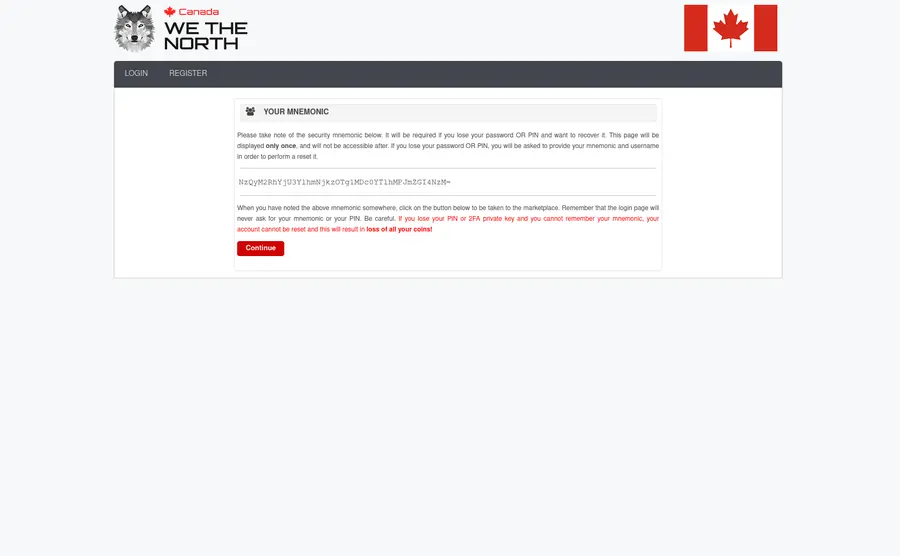
Seed phrase storage: write the 25-word Monero mnemonic on paper. Store it offline. Never photograph it, never type it into a cloud note, never paste it into a chat. Use KeePassXC for your wallet passphrase, with the KeePassXC database itself on an encrypted drive.
Generate a PGP key pair and upload the public key
PGP (Pretty Good Privacy) is the encryption standard used across privacy network markets for vendor communications. Wethenorth requires vendors to use PGP 2FA. As a buyer, uploading a public key to your profile lets vendors send you encrypted order confirmations and shipping updates that only you can read.
Install GnuPG — Gpg4win on Windows, GPGTools on macOS, or the gnupg package on any Linux distribution. Generate a 4096-bit RSA key pair. Export the public key block (the ASCII-armoured text starting with -----BEGIN PGP PUBLIC KEY BLOCK-----) and paste it into your Wethenorth profile settings.
Keep your private key offline wherever possible. Losing the private key means losing the ability to decrypt anything encrypted to your key — including any message a vendor ever sends you. Store it in KeePassXC with a long, random passphrase. Back that passphrase up on paper, stored separately from the database file.
You do not need PGP to browse or buy on Wethenorth. But vendors with strong reputations will often require it for communications about delivery addresses. Set it up before your first order.
PGP verification: when you receive a message claiming to be from a vendor, paste it into GnuPG and verify the signature against the vendor's public key (visible on their market profile). A forged message cannot produce a valid signature. Privacy Guides has a practical PGP primer that covers the full verification workflow.
Choose your operating system posture
For casual reading — checking the market, reviewing listings — a hardened laptop running Tor Browser on Safest is sufficient. For purchases, the level of care increases.
The standard recommendation for Canadian buyers making purchases is Tails OS booted from a USB drive. Tails is an amnesic operating system — every session starts from a clean state, leaves no trace on the host computer, and routes all connections through Tor automatically. A $10 USB drive and a one-time setup is the entire cost. For deliveries going to your real address, Tails meaningfully reduces the digital footprint associated with each transaction.
Power users layer Whonix inside Qubes OS. Whonix routes everything through Tor at the operating system level; Qubes isolates each application in a separate virtual machine. The combination is the gold standard for operational security. It requires dedicated hardware and a learning curve.
Public WiFi is acceptable for browsing — coffee shops, libraries — but pair it with Mullvad VPN on your device before connecting Tor. The chain becomes: public WiFi → VPN → Tor → Wethenorth. Encrypt your laptop storage with VeraCrypt. Use Signal for any off-market communication. Use Proton Mail if an email is ever needed. These are not paranoid extremes — they are standard operational defaults for anyone transacting on Canadian privacy network markets in 2026.

Everything you need, in one table
These are the tools mentioned in the guide above. All are free and open-source. Use the official links only — never search for these in an app store without verifying the publisher.
| Tool | Purpose | Platform | Official source |
|---|---|---|---|
| Tor Browser | Access .onion addresses | Windows, macOS, Linux, Android | torproject.org |
| Cake Wallet | Monero self-custody (mobile) | Android, iOS | cakewallet.com |
| Feather Wallet | Monero self-custody (desktop) | Windows, macOS, Linux | featherwallet.org |
| GnuPG | PGP encryption and key management | Windows, macOS, Linux | gnupg.org |
| KeePassXC | Password and key storage (offline) | Windows, macOS, Linux | keepassxc.org |
| Tails OS | Amnesic OS via USB, routes all traffic through Tor | USB boot (any computer) | tails.net |
| Mullvad VPN | VPN layer before Tor on public WiFi | Windows, macOS, Linux, Android, iOS | mullvad.net |
| VeraCrypt | Full-disk and volume encryption | Windows, macOS, Linux | veracrypt.eu |
| Signal | Encrypted messaging for off-market contact | Android, iOS, desktop | signal.org |
Pre-order checklist
Before placing your first order on Wethenorth, verify all eight of these items.
- Tor Browser installed and verified, security set to Safest
- Link copied from this page or verified via PGP-signed Dread announcement
- Self-custody XMR or BTC wallet set up, seed phrase backed up offline
- Funds transferred from exchange to self-custody wallet before any market deposit
- PGP key pair generated, public key uploaded to Wethenorth profile
- KeePassXC database created for all credentials and key passphrases
- Tails OS USB created (or Whonix/Qubes for higher threat model)
- Invite received from a Dread-verified community member (not purchased)
Ready to connect to Wethenorth market?
Both verified mirrors are on the mirrors directory page with individual copy buttons and last-verified dates. Bookmark it. Check back when mirrors rotate.
Common questions about accessing Wethenorth
Does Wethenorth require JavaScript to function?+
Wethenorth market was built to work without JavaScript. You can set Tor Browser to Safest — which disables JS — and the login page, captcha, and market interface all load normally. This is by design: a site that demands you enable scripting before it renders is a red flag in the privacy network context. Real WTN renders fine at Safest. If you reach a page that blocks access until you enable JavaScript, you are almost certainly looking at a phishing clone.
How long does it take to get a Wethenorth invitation?+
Variable. Buyers who build a genuine Dread presence over two to four weeks — contributing to threads, reviewing vendors in other markets, participating in security discussions — typically receive an invitation within days of asking. Accounts that appear to exist solely to request codes get ignored. There's no shortcut. The waiting period is part of the security model. Plan for four to six weeks from first Dread registration to receiving a valid WTN invite code.
Is Monero required or can I use Bitcoin on Wethenorth?+
Both are accepted. Monero provides stronger privacy at the protocol level — transactions do not appear on a public blockchain and amounts are hidden. Bitcoin is easier to acquire through Canadian exchanges but your transaction graph is permanently visible. Many experienced Canadian buyers convert a portion of their BTC to XMR through a swap service before depositing to the market. For your first order, use whichever you already hold in a self-custody wallet. The key rule is identical for both: never deposit directly from an exchange.
What happens if both mirrors are slow or unreachable?+
Tor circuits fail for reasons unrelated to the destination. Before concluding that Wethenorth is down: right-click the URL bar and select New Tor circuit for this site, then wait 30 seconds and reload. Try the second mirror. Try at a different time of day — mornings in Eastern Time tend to have less Tor network congestion. If both mirrors remain unreachable after eight genuine attempts across two hours, check /d/WeTheNorth on Dread. Real outages are always posted within minutes. The admins post PGP-signed status updates during any extended maintenance window.
Do I need Tails or can I use my regular laptop?+
Your regular laptop with Tor Browser on Safest is adequate for reading and browsing. For orders — particularly anything going to a real delivery address — Tails OS meaningfully reduces the persistent forensic footprint on your device. It also eliminates the risk of keyloggers or other malware that may exist on a general-purpose computer. A Tails USB costs $10 and 20 minutes to set up. The risk/cost ratio strongly favours using it for any purchase. That said, many Canadian buyers use hardened regular laptops with full-disk encryption and have no issues — the right posture depends on your individual threat model.
Can I use a VPN together with Tor to access Wethenorth?+
The chain that works: your device → VPN → Tor → Wethenorth. This is sometimes called VPN over Tor and is useful when your ISP or network blocks Tor exit nodes directly, or when you're on public WiFi and want to hide that you're using Tor from the WiFi operator. Mullvad is the standard recommendation because it accepts Monero and doesn't log connection metadata. Do not do it the other way around (Tor over VPN) — routing Tor through a VPN exit node gives the VPN provider visibility into your Tor usage. The Tor Project's own guidance says VPN before Tor is acceptable for specific use cases and neutral in most others.
What is the legal situation for Canadian buyers in 2026?+
Accessing a privacy network marketplace is not itself an offence under Canadian federal law. Transacting for controlled substances is — the Controlled Drugs and Substances Act is explicit. Canadians have been charged in connection with privacy network market purchases primarily through parcel interception, not through Tor surveillance. Wethenorth's domestic-only design means packages never cross a border and therefore skip the layer of customs inspection that triggers the majority of international privacy network prosecutions. That reduces risk. It does not eliminate it. This page provides information. It is not legal advice. Consult a criminal defence attorney licensed in your province before making any decisions.
How does Wethenorth escrow work for buyers?+
Standard escrow. Funds are held by the platform between the moment you pay and the moment you confirm delivery. Vendors cannot access your payment until you click order received or the auto-complete window closes (typically after 14 days without a dispute). If something goes wrong — package doesn't arrive, wrong item — open a dispute before clicking confirm. The platform mediates. There is no Finalize Early option on Wethenorth, which keeps the incentive structure honest for both parties. Monero deposits settle in roughly 20 minutes; Bitcoin requires three confirmations, usually under an hour.
Where can I find more information about Wethenorth vendors?+
The /d/WeTheNorth subboard on Dread is the primary community hub. Vendor reviews, reputation threads, and admin announcements all live there. Within the market itself, every vendor has a public feedback score tied to verified transactions — not self-reported ratings, actual completed orders. New buyers should spend time reading vendor profiles and feedback before placing an order. For general background on the platform, read our origin page and the mirrors directory for verified access points.
